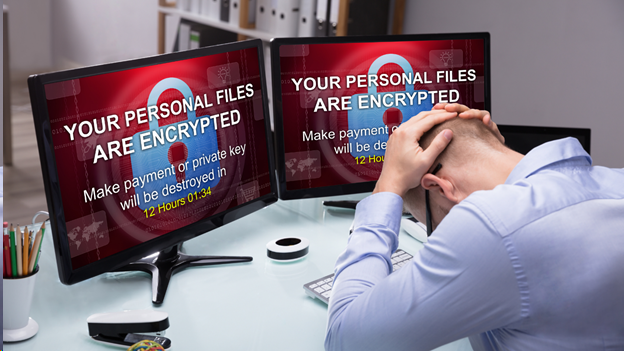
As organizations are becoming more aware of Cyber-attacks and Ransomware and are improving IT security tools they use; Ransomware and Cyber criminals are also evolving and are devising new ways to breach a company's systems. In addition, expenses related to Cyber breaches/attacks are steadily increasing. Ponemon's 2019 Cost of a Data Breach study noted that "breaches originating from a malicious Cyber-attack were not only the most common, but also the most expensive."
Below are several tips to help combat Ransomware and other Cyber threats:
- Strong passwords aren't enough - companies should be implementing and enforcing two factor authentication to prevent unauthorized access using a company account, especially for users with elevated access rights.
- "Over the counter" anti-virus is a bit outdated - look into rolling out Endpoint Detection and Response (EDR) software. It's smarter and responds fast to threats than your average anti-virus software.
- Implement Email Spam Filtering - a quality spam Filtering service will not catch all spam and phishing attempts but it will prevent most of them from reaching a user's inbox; therefore reducing the threat that a user errantly clicks on a malicious link For the ones that do get through, educate your staff on how to identify and deal with phishing attempts.
- Introduce multiple point of redundancy - in some cases your backup system may be compromised or unavailable. Remember, cloud servers and backup systems can get hit with ransomware too. It's best to have a backup to your backup.
- Patch servers and computers regularly and update firmware on hardware devices.
Last but not least, make sure you have adequate Cyber insurance that covers ransomware events, extortion payments, legal and forensic fees and data recovery in additioon all of the other beneficial coverages that are provided by a Cyber Liability policy.





 As, risk managers, we often get asked by clients, “what is the appropriate period to retain insurance policies” - the easy answer is “forever”... You are probably thinking that guidance seems a bit excessive, however quite a few types of policies, such as commercial general liability, may be triggered long after the policy has expired and thus should not be discarded but rather meticulously tracked.
As, risk managers, we often get asked by clients, “what is the appropriate period to retain insurance policies” - the easy answer is “forever”... You are probably thinking that guidance seems a bit excessive, however quite a few types of policies, such as commercial general liability, may be triggered long after the policy has expired and thus should not be discarded but rather meticulously tracked.