Risk Identification is the first of three phases that make up a Risk Assessment.
Risk Assessment at a Glance
An organization-wide Risk Assessment doesn’t have to be overwhelming. Risk Assessments can be made manageable by addressing the three distinct phases: Risk Identification, Risk Analysis and Risk Evaluation. The phases allow you to focus specific groups of people on specific tasks. The following is a brief rundown on the three phases and the groups and tasks involved.
Risk Identification describes the risks so that each can be classified into their appropriate risk categories. Managers representing the various departments and functions in the organization identify the objectives of their respective groups and the risks to achieving those objectives.
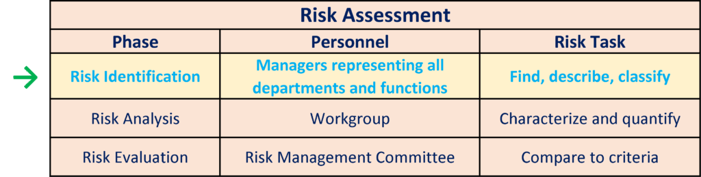
Risk Analysis characterizes the risks, classifies them into the appropriate Risk Categories, quantifies likelihood and impacts, and enters this information into the Risk Register. The Workgroup, a body of managers with detailed, day-to-day knowledge of the operations and risks of the organization, conducts this phase.
Risk Evaluation compares the risks to the relevant Risk Tolerances and prioritizes risks for treatment. The Risk Management Committee (RMC), a group of key executives responsible for the organization’s operations and performance handles this step.
Risk Identification: Who to Turn to
Risk Identification may at first appear to be a far-ranging thought exercise meant to create an exhaustive list of every possible threat; however, maintaining a big picture view allows you to take a priority approach to identifying risks:
- Identify critical processes and critical paths, for example, a dispatch system or a high-value truck route.
- Consider the effects of various amounts of downtime for each system and process. What are the effects of one hour of downtime? One day? One week? Determine the maximum amount of downtime that can be tolerated.
- Identify most likely threats and what weaknesses each would exploit.
In the Risk Identification phase, you are looking for managers with expert knowledge of the business. Ensure that your pool of contributing managers represents all of the significant departments and functions: Human Resources, Accounting and Finance, Operations, IT, Supply Chain Management, etc. Risk Identification is also greatly aided by utilizing the special expertise of the staff of the compliance functions: Legal Affairs, Internal Audit and Regulatory Compliance.
The contributing managers describe why and how each risk event could prevent, impair, or delay the achievement of an objective. These managers will also describe what circumstances would allow the threat to be realized. Knowing those circumstances will help to quantify the likelihood of the risk event.
Risk Identification Tools
Questionnaires and checklists can be designed specifically for ERM. The best ones are brief, so as to encourage completion. The best ones also ask about objectives as well as risks. A hallmark of ERM is that risks are aligned with the objectives of the organization.
Workshops provide opportunity to analyze objectives and stakeholder interests and find the range of risks that apply to each. This method of identifying risks ensures alignment of risk management with organization objectives. It also takes advantage of having risk management experts present to facilitate the discussions.
Inspections and audits surface weaknesses in processes and provide root cause analysis and recommendations. These enhancements translate into information about both the risks and the potential mitigations.
Flowcharts and dependency analyses identify critical pathways, the first step in Risk Identification.
HAZOP (Hazard and Operability studies) and FMEA (Failure Mode Effects Analysis) are specifically tailored to assessing technologies.
SWOT (Strengths, Weaknesses, Opportunities and Threats) analyses and PESTLE (Political, Economic, Sociological, Technological, Legal and Environmental) analyses are often already in use to run the business and happen to serve ERM purposes very well. They are already tuned to the achievement of objectives and discerning the related obstacles.
Takeaways
Keep these three principles in mind to guide you to a successful Risk Identification phase.
- Representation from significant departments positions your ERM initiative to build the appropriate universe of risk information.
- Amassing appropriate expert knowledge will ensure the identification of critical processes, likely threats, weaknesses and potential mitigations.
- Considering objectives and stakeholder interests as well as risk and mitigation information is critical for well-executed Risk Identification.

)